Results of 2nd period
Summary of the context and overall objectives of the project
The vision of FutureTPM was to provide a new generation of TPM-based solutions, incorporating robust and physically secure Quantum-Resistant (QR) cryptographic primitives, to ensure long-term security, privacy and operational assurance in the complex domain of future ICT systems and services. The goal was to enable a smooth transition from current TPM environments, based on traditional cryptography, to systems providing enhanced security through QR cryptographic functions, including secure authentication, encryption and signing functions, thus, turning the host device into a “hardened” security token that may also remain secure long-term against an enhanced threat landscape in quantum computing deployments. By selecting current state-of-the-art QR algorithms (and designing new schemes) for primitives like Key Management, Encryption, Signatures, Hash-Functions, Message Authentication Codes (MACs) and Direct Anonymous Attestation (DAA), FutureTPM comes to fill the perceived gaps in the current status of cybersecurity. This enabled the integration and evaluation of this new-generation QR TPM to a number of vertical applications, thus, generating a secure root of trust that can be used for e.g., interacting with cloud services, accessing corporate services and performing banking and eCommerce transactions. For each primitive, detailed attention was paid towards investigating a security threat model, formalizing security properties and providing formal proofs. This architecture was also enhanced with detailed threat modelling and risk assessment (both during design- and run-time) functionalities so as to provide a holistic TPM-backed solution capturing the strict security and privacy requirements of all deployed edge and infrastructure assets considered in various application domains. Accompanying with the QR TPM design and implementation, the FutureTPM project was able to show-case the benefits of such a decentralized root of trust in three use cases (namely ePayment, Activity Tracking and Device Management), which were used to validate the feasibility and performance of the FutureTPM solution in these three selected real-world systems that may be affected by the advent of quantum computing as a threat to security.
Work performed from the beginning of the project to the end of the period covered by the report and main results achieved so far
In the FutureTPM project, we have investigated technical and security, privacy and operational assurance requirements for the new generation of the TPM-based solutions that are secure against the future large-scale quantum computer attacks. We have also conceptualized three industry-driven use cases that will allow the validation of the project research results in real-world scenarios and how the overall FutureTPM solution can serve vertical industry needs.
We have also identified a set of QR cryptographic primitives which could replace all of the classes of crypto algorithms supported by the existing TPM technology. Our selection is based on the state-of-the-art researches in the Post-Quantum Cryptography (PQC) field; for example, several digital signatures, asymmetric encryption and key exchange mechanisms are chosen from the latest round of the NIST PQC standardisation process. This set of selected cryptographic mechanisms will be implemented in one of the three TPM environments; namely SW-, HW- and Virtual-based TPM.. In this line of research, the FutureTPM consortium has also designed two lattice-based Direct Anonymous Attestation (DAA) schemes. DAA is an important cryptographic primitive that was originally designed to support user privacy when using a TPM chip. The QR DAA research has not yet been covered by existing standardization efforts. We have implemented one of these two schemes in a software-based TPM environment and we will implement the other DAA variant in the second part of the project.
Furthermore, the project also completed the modelling and formal verification of one of the core services towards building chains of trust based on the secure identification and correct configuration state of deployed devices. The concept of secure remote attestation and all its relevant functionalities was verified such as the creation of the TPM keys, the Enhanced Authorization (EA), and the management of sessions and Platform Configuration Registers. This was also accompanied with a detailed abstraction of the TPM’s building blocks as ideal functionalities and trusted platform command abstractions consisting of specific set of formally specified primitives sufficient to implement the core TPM functionalities beyond the crypto operations. Such a “bottom-up” modelling approach y, based on the use of trusted abstract platform models and idealized functionalities, is more than just a set of proofs of correctness of specific services but it can also enable the security modelling of the TPM as a whole merging various functionalities offered by the different abstraction layers.
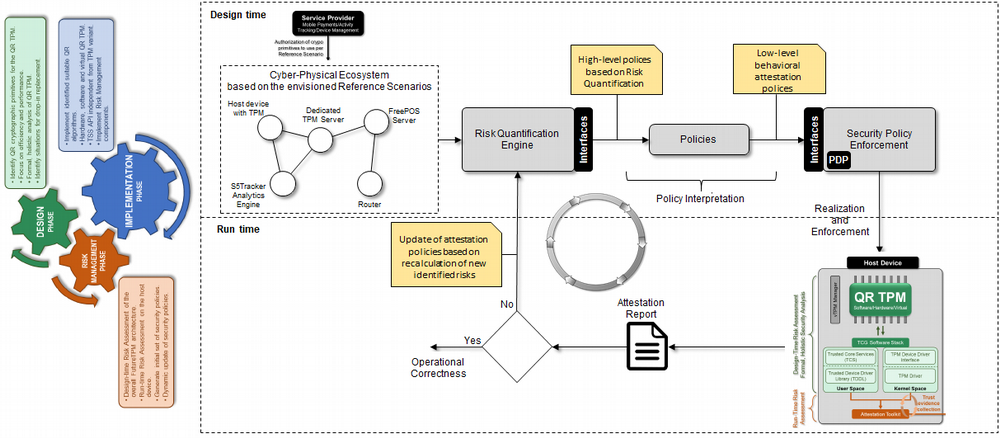
Research has culminated to the development of holistic risk assessment framework capable of providing functionalities during both design-time, where an initial risk graph of all possible threats and risks are identified, and run-time, where the risk graph can be updated in order to achieve the required security, trust and privacy properties in the case of newly identified (e.g., zero-day) vulnerabilities.
We have implemented several selected QR cryptographic mechanisms (WP5), with detailed evaluation results been available. A detailed testing was also conducted in the context of the envisioned use cases. An on-boarding of this set of enriched use cases, in the overall FutureTPM framework, was concluded, leading to promising outcomes with regards to the validity of TPM-backed solutions to serve vertical industry needs.
Finally, regarding dissemination, awareness, and standardization activities, it is worth noting the great effort of FutureTPM consortium in clustering with other EU security- and privacy-related research project activities (e.g., PROMETHEUS, PAPAYA, and ASTRID) towards improving “cyber security”. For the latter, a number of actions were taken for the promotion of the project results to the trusted computing community and close follow-up of standardization activities
1.3 Progress beyond the state of the art and expected potential impact (including the socio-economic impact and the wider societal implications of the project so far)
The FutureTPM project has drawn a lot of attention from the trusted computing community towards increasing the trustworthiness of ICT services and products. Based on the information from the Trusted Computing Group (TCG), more than a billion devices already use the TPM technologies. Virtually all enterprise personal computers, many servers and embedded systems include the TPM. Furthermore, all related TCG technologies, such as self-encrypting drivers and network security specifications have been used by networking equipment and other devices. All of these systems and applications will directly benefit from the research results produced from the FutureTPM project.
Except from trusted computing, this project also has a strong impact on other applications of applied cryptography in general. For any application, which requires long-term security for data protection and user privacy, it can follow the outputted research results and technical guidance from this project to make a smooth transition from today’s cryptographic mechanisms to post-quantum cryptographic solutions.